Upgrade & Secure Your Future with DevOps, SRE, DevSecOps, MLOps!
We spend hours scrolling social media and waste money on things we forget, but won’t spend 30 minutes a day earning certifications that can change our lives.
Master in DevOps, SRE, DevSecOps & MLOps by DevOps School!
Learn from Guru Rajesh Kumar and double your salary in just one year.
In the early days of infrastructure, security was a physical perimeter—a literal wall around the server room. Today, our infrastructure is code, our servers are ephemeral containers, and our perimeter is an API. In this fluid environment, the traditional “security guard” is replaced by the “security engineer” who understands that a single misconfiguration in a YAML file can be the difference between a secure deployment and a catastrophic breach.
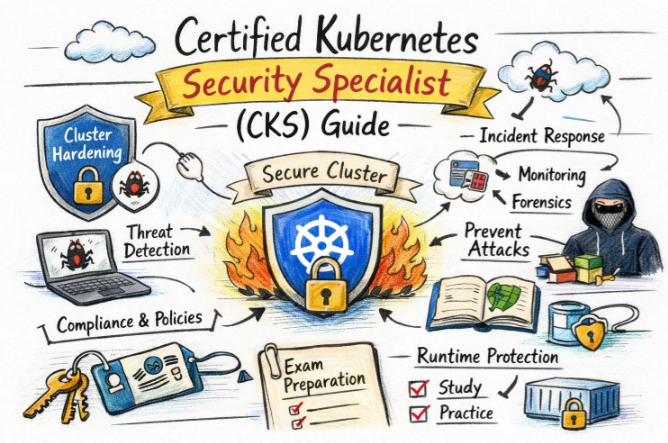
The Certified Kubernetes Security Specialist (CKS) is not just another badge for your LinkedIn profile. It is a rigorous validation that you possess the “defense-in-depth” mindset required to protect modern, cloud-native workloads. This guide outlines the strategic path to mastering Kubernetes security and how it elevates your career in the global engineering market.
Navigating the CNCF Certification Map
Understanding where you stand in the Kubernetes ecosystem is the first step toward mastery. The CKS is an advanced specialization, and its value is rooted in the foundational knowledge that precedes it.
Strategic Certification Comparison
| Certification | Level | Focus Area | Prerequisites | Career Target | Recommended Order |
| CKAD | Intermediate | Application Design | None | App Developers | 1st (for Devs) |
| CKA | Intermediate | Infrastructure Admin | None | SREs / Admins | 1st (for Ops) |
| CKS | Advanced | Security Hardening | Active CKA | DevSecOps / Lead | 2nd (Must have CKA) |
Deep Dive: The Certified Kubernetes Security Specialist (CKS)
The CKS is a performance-based challenge. It doesn’t ask you what a NetworkPolicy is; it asks you to write one that stops an active lateral movement attack in a live cluster.
What it is
The CKS validates a practitioner’s ability to secure container-based applications and the Kubernetes platforms they inhabit. It spans the entire lifecycle of a workload—from the initial build and supply chain security to the deployment phase and ongoing runtime monitoring. It is widely considered one of the most difficult and rewarding exams in the cloud-native space.
Who should take it
- Security Engineers looking to specialize in container security.
- DevOps & DevSecOps Engineers who want to lead “Shift Left” initiatives.
- Platform Engineers building internal developer platforms with baked-in security.
- Engineering Managers who need to audit the risk profiles of their technical stacks.
Skills you’ll gain
Preparing for the CKS fundamentally changes how you view a cluster. You stop seeing it as a platform for apps and start seeing it as a surface area to be protected.
- Cluster Hardening: Securing the control plane, using RBAC to enforce the principle of least privilege, and protecting sensitive secrets.
- System Hardening: Reducing the attack surface of the underlying host through Seccomp, AppArmor, and minimizing OS-level vulnerabilities.
- Supply Chain Security: Implementing trusted image registries, scanning for CVEs, and using Admission Controllers to block non-compliant workloads.
- Microservice Security: Isolating pods via Network Policies and ensuring encrypted, authenticated communication between services.
- Monitoring & Auditing: Leveraging tools like Falco to detect anomalies at the kernel level and performing deep-dive audits of cluster activity.
Real-World Mastery: What You’ll Do After CKS
Holding the CKS credential means you have the technical hands to implement high-level security policies.
- Hardening Kubernetes Environments: You will be able to take a “vanilla” cluster and transform it into a hardened environment that passes enterprise-grade compliance audits.
- Automated Security Pipelines: You can design CI/CD workflows that automatically reject images with critical vulnerabilities before they ever hit production.
- Runtime Defense: You’ll be capable of deploying runtime security monitors that alert on suspicious shell executions or unauthorized file modifications in real-time.
- Zero-Trust Networking: You will have the skills to design pod-to-pod communication rules that ensure even if one service is compromised, the rest of the cluster remains safe.
The Preparation Blueprint
- 7–14 Days (The Specialist): For those who live in the CLI. Focus on the nuances of the CKS curriculum and the specific syntax of third-party tools like Falco and Trivy.
- 30 Days (The Professional): The ideal timeline. Spend two weeks on theoretical deep-dives into Linux security and two weeks on high-speed laboratory practice.
- 60 Days (The Foundation Builder): Recommended if you are new to the security domain. Use the first month to master the Linux kernel security features before moving into Kubernetes-specific configurations.
Professional Pitfalls
- The “Search” Trap: You have access to official docs, but time is your biggest enemy. If you haven’t memorized basic NetworkPolicy and RBAC structures, you will likely run out of time.
- Ignoring the OS: The CKS is as much about Linux security as it is about Kubernetes. Failing to understand how a container interacts with the host kernel (Syscalls) is a common reason for failure.
- CKA Rustiness: Because CKA is a prerequisite, many assume they remember the basics. However, you must be able to troubleshoot cluster networking and node failures quickly to clear the security tasks.
Choose Your Professional Evolution
The CKS is a versatile asset that opens doors into several high-growth specialized domains.
6 Specialized Career Paths
- DevOps Path: Focuses on the efficiency of the delivery pipeline. CKS knowledge ensures that speed never compromises safety.
- DevSecOps Path: The most direct career move. You become the subject matter expert on integrating automated security into every stage of development.
- SRE Path: Focuses on the “Reliability” side of security. Hardening clusters to ensure that malicious actors cannot cause system-wide outages.
- AIOps/MLOps Path: Securing the massive data pipelines and high-performance clusters required for modern artificial intelligence and machine learning.
- DataOps Path: Protecting the integrity and privacy of data as it moves through containerized analytics platforms.
- FinOps Path: Understanding the cost of security resources and ensuring that “cloud sprawl” doesn’t create both financial and security risks.
Role → Recommended Certification Roadmap
| Your Role | Core Credential | The Next Strategic Step |
| DevOps Engineer | CKA / CKAD | CKS (To move into Lead/SecOps roles) |
| SRE | CKA | CKS / Prometheus (PCA) |
| Platform Engineer | CKA | CKS / Terraform Certification |
| Cloud Engineer | CKA | AWS / Azure / GCP Security Specialty |
| Security Engineer | CKS | CCSP / CISSP (for management track) |
| Data Engineer | CKAD | Spark / Kafka certifications |
| FinOps Practitioner | FinOps Cert | CKA (to understand technical resource usage) |
| Engineering Manager | CKA | CKS (to lead security-conscious teams) |
Top Training & Mentorship Institutions
Preparing for a performance-based exam requires hands-on labs and expert guidance. Here are the leading institutions for Kubernetes training:
- DevOpsSchool: A global leader in DevOps education, offering instructor-led, lab-intensive CKS programs that focus on clearing the exam on the first attempt.
- Cotocus: Specializes in corporate training and cloud-native consulting, providing deep insights into securing large-scale production environments.
- Scmgalaxy: A vast community platform offering mock exams and specialized tutorials that help candidates build the speed required for the CKS terminal.
- BestDevOps: Known for their expert-led bootcamps, they provide a structured approach to mastering the complex tools found in the CKS curriculum.
- DevSecOpsSchool: The primary destination for security-focused engineers, offering courses that integrate CKS concepts with the broader DevSecOps lifecycle.
- SRESchool: Focuses on the intersection of uptime and security, helping engineers build clusters that are both resilient and hardened.
- AIOpsSchool: Tailored for the next generation of engineers who are securing AI and ML workloads on Kubernetes.
- DataOpsSchool: Bridges the gap between data engineering and infrastructure security, focusing on data isolation and storage encryption.
- FinOpsSchool: Teaches the financial governance of cloud-native systems, ensuring your security posture is also cost-effective.
FAQ: CKS Career & Strategy
1. Is CKS worth the effort?
Absolutely. In the current market, “Security-Aware Kubernetes Engineers” are among the most sought-after and highest-paid professionals in the tech industry.
2. Can I take CKS without CKA?
No. You must have an active CKA certification. If your CKA has expired, you must renew it before your CKS can be officially granted.
3. What is the passing score?
You must score 67% or higher on the performance-based tasks within 120 minutes.
4. How long is the certification valid?
It is valid for 2 years, reflecting the fast-paced nature of the Kubernetes security landscape.
5. How difficult is it compared to other security certs?
Most consider it harder than multiple-choice exams like CISSP because it requires you to actually perform the security configuration, not just know the theory.
6. Do I need to learn Falco and Sysdig?
Yes, understanding runtime security tools like Falco is a significant part of the CKS domain.
7. Is there a free retake?
Most official vouchers (including those from training partners like DevOpsSchool) offer one free retake.
8. Can I use a calculator or notes?
No. You only have access to a single terminal and the official allowed documentation in a separate browser tab.
9. What is the best way to practice?
Killer.sh and mock labs provided by training institutions are the best ways to simulate the pressure of the 2-hour exam window.
10. Why is the time limit so tight?
To ensure you have “muscle memory.” In a real security incident, every minute counts; the exam reflects that reality.
11. Does it help with remote jobs abroad?
Yes. CNCF certifications are globally recognized standards, making it much easier to prove your technical competence to international employers.
12. What if I am a manager?
Taking the CKS gives you the technical depth to understand the risks your team faces and to better justify the budget for security tooling.
FAQ: Certified Kubernetes Application Developer (CKAD)
1. Is CKAD only for developers?
While designed for developers, it is excellent for anyone who wants to master how applications run in K8s. It is a perfect precursor to CKA/CKS.
2. How long does CKAD take to study?
If you are already a developer using Docker, 2 to 3 weeks of focused practice on kubectl is usually sufficient.
3. What is the value of CKAD in the market?
It proves you are a “Cloud Native Developer” who can package, deploy, and monitor their own services without needing a separate Ops team.
4. Is the CKAD exam also performance-based?
Yes. Like CKA and CKS, you are given a real cluster and a set of problems to solve.
5. Does CKAD cover security?
It covers basic application security (Secrets, ConfigMaps, ServiceAccounts), but it doesn’t go into the depth of hardening that CKS does.
6. Can I use documentation during CKAD?
Yes, you have access to the official Kubernetes documentation during the exam.
7. What are the common topics for CKAD?
Expect a heavy focus on Pod Design, Multi-container pods, CronJobs, and troubleshooting application-level logs.
8. How many years is CKAD valid?
It is valid for 3 years from the date of passing.
Post-CKS Evolution: What’s Next?
According to industry trends observed by GurukulGalaxy, a specialist’s education is never truly complete. Once you have cleared the CKS, consider these three paths to maintain your competitive edge:
- Vertical Specialization: Prometheus Certified Associate (PCA). You cannot secure what you cannot see. Mastering observability is the natural next step after security.
- Horizontal Expansion: HashiCorp Certified: Terraform Associate. Security begins with the infrastructure. Learn to provision your hardened clusters using Infrastructure as Code (IaC).
- Strategic Leadership: Certified Cloud Security Professional (CCSP). If you are moving toward a Chief Information Security Officer (CISO) or Architect path, the CCSP provides the high-level governance needed to manage enterprise-wide risk.
Conclusion
The journey toward the Certified Kubernetes Security Specialist is one of the most transformative paths an engineer can take. It moves you away from simply “building things that work” toward “building things that last.” In a world where cyber threats are becoming increasingly sophisticated, the ability to architect, harden, and monitor a Kubernetes cluster is a rare and invaluable skill set. By committing to this certification, you are doing more than just passing an exam; you are joining an elite group of professionals dedicated to the safety and integrity of the digital world. The path is demanding, the exam is fast, but the career trajectory and the technical confidence you gain are unparalleled. Whether you are an engineer in India or working globally, the CKS is your passport to the future of secure cloud-native engineering.