Upgrade & Secure Your Future with DevOps, SRE, DevSecOps, MLOps!
We spend hours scrolling social media and waste money on things we forget, but won’t spend 30 minutes a day earning certifications that can change our lives.
Master in DevOps, SRE, DevSecOps & MLOps by DevOps School!
Learn from Guru Rajesh Kumar and double your salary in just one year.
When we first started moving workloads to Kubernetes, the focus was almost entirely on making sure things actually worked. We wanted our pods to run, our services to be reachable, and our deployments to scale. But as these systems grew, so did the risks. Today, a functional cluster isn’t enough; it must be a fortress.
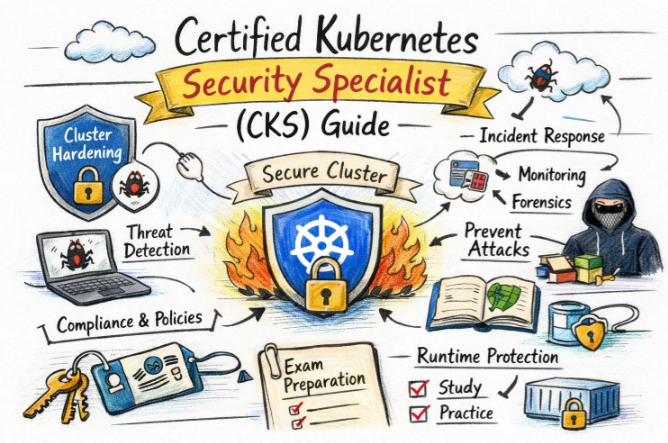
The Certified Kubernetes Security Specialist (CKS) is the certification that proves you have moved beyond basic administration. It is a vital component of the Master in Observability Engineering Certifications Program, focusing on the reality that you cannot truly observe or manage a system if you cannot keep it secure. Whether you are an engineer in a startup in Bangalore or a manager in a global tech firm, this path is about building systems that are resilient against modern threats.
The Architecture of Engineering Certifications
A career isn’t built on a single exam. It is built on a series of steps that add layers to your expertise. The following table shows how the CKS fits into the broader landscape of professional development.
| Track | Level | Who it’s for | Prerequisites | Skills Covered | Recommended Order |
| DevOps | Foundation | Engineers, Devs | Basic Linux | Automation, CI/CD | 1 |
| SRE | Specialist | Reliability Leads | CKA | SLOs, Monitoring | 2 |
| Kubernetes | Professional | Admins, SREs | Linux Skills | Cluster Management | 3 |
| Security | Expert | Security Leads | CKA | CKS, Hardening | 4 |
| DevSecOps | Expert | Architects | CKS, CKA | Lifecycle Defense | 5 |
| Observability | Master | Technical Leads | SRE, CKS | Full System Viz | 6 |
Understanding the CKS: The Guardian’s Mindset
The CKS is a performance-based exam. This means there are no multiple-choice questions. You are given a set of problems and a live terminal. You must find the vulnerability, fix it, and verify that the system is now safe without breaking the application logic.
What it is
The Certified Kubernetes Security Specialist (CKS) is a high-level certification that focuses on the security of the containerized environment. It covers the entire lifecycle of an application—from how it is built and stored to how it is deployed and monitored while running. It is the industry’s way of ensuring that an engineer can handle the security complexities of a Kubernetes cluster in a production setting.
Who should take it
If you are already a Certified Kubernetes Administrator (CKA), this is your next logical step. It is designed for Software Engineers, DevOps Professionals, and Security Engineers who are responsible for production clusters. It is also highly recommended for Engineering Managers who want to understand the security posture of their infrastructure and guide their teams toward better practices.
Skills you’ll gain
Preparing for the CKS forces you to think like a “defender.” You stop taking default configurations for granted and start verifying every layer of your stack.
- Cluster Hardening and Setup: You will learn to secure the “brain” of the cluster (the API server), use CIS benchmarks to find configuration gaps, and manage administrative access with highly granular RBAC rules.
- Host-Level Security: You will gain the ability to lock down the Linux nodes that run your containers, using kernel-level tools like AppArmor and Seccomp to prevent unauthorized system calls.
- Supply Chain Defense: You’ll master the art of “trusted images.” This means scanning for vulnerabilities before deployment, signing images to ensure they haven’t been tampered with, and using Admission Controllers to enforce these rules.
- Runtime Protection: You will learn how to monitor a running cluster for suspicious activity. If a process starts acting strangely or a sensitive file is accessed, you will know how to detect it and respond instantly.
Real-world projects you should be able to do after it
The goal of this certification is to give you the skills to lead high-impact security projects within your organization.
- Designing a “Secure-by-Default” Platform: You will be able to build a Kubernetes environment where security is built-in, not bolted on. This includes automated network isolation and encrypted secrets storage from day one.
- Implementing a Vulnerability Management Program: You can set up automated systems that scan every piece of code and every container image. If a security flaw is detected, the deployment is blocked before it can ever reach a server.
- Advanced Incident Detection: You will have the skills to implement runtime security tools that alert your team the moment a pod is compromised, allowing for rapid containment and investigation.
Preparation Plan
7–14 Days (The Expert Sprint):
This is for those who live and breathe Kubernetes security every day.
- Phase 1: Drill down into tool-specific commands for Falco, Trivy, and Cosign.
- Phase 2: Practice manual edits to the API server and Kubelet configurations.
- Phase 3: Master the use of the official documentation for quick YAML lookups.
30 Days (The Standard Path):
- Weeks 1-2: Focus on the internal Kubernetes security primitives: RBAC, Network Policies, and Admission Controllers.
- Week 3: Move to the host and runtime level: AppArmor, Seccomp, and auditing.
- Week 4: Take multiple mock exams. Focus on your typing speed and accuracy in the terminal.
60 Days (The Deep Dive):
- Month 1: Focus on the “First Principles.” Learn how the Linux kernel handles container isolation. Read the documentation for every security flag in the Kubernetes API.
- Month 2: Follow the 30-day path above, but spend twice as much time on “breaking” the cluster to see how the security tools respond.
Common Mistakes
Even very senior engineers fail the CKS because they treat it like a theory test.
- Ignoring the “Clock”: You have 2 hours to solve complex tasks. If you spend 20 minutes on a single pod’s security context, you won’t finish the exam. Learning when to move on is vital.
- Documentation Fatigue: You are allowed to use the official documentation. However, if you don’t know exactly what to search for, you will waste precious minutes reading long articles instead of finding the one YAML snippet you need.
- Context Errors: The exam has several clusters. If you fix a problem on “Cluster A” but the question asked for “Cluster B,” you get zero points. Always double-check your cluster context before running a command.
Best Next Certification After CKS
Winning the CKS is a major milestone, but it opens doors to even more specialized paths.
- Same Track: Certified DevSecOps Professional. This expands your security knowledge into the developer’s workstation and the CI/CD pipeline.
- Cross-Track: Cloud Security Specialist (AWS/Azure/GCP). This allows you to secure the underlying virtual machines and networks that Kubernetes runs on.
- Leadership: Master in Observability Engineering. This is the highest level, where you learn to combine security, reliability, and performance into a single, visible strategy.
Choose Your Path: 6 Professional Learning Tracks
- DevOps Path: Focuses on making software delivery fast and reliable. CKS is the guardrail that ensures speed doesn’t lead to disasters.
- DevSecOps Path: This is for those who want to be dedicated security architects within a cloud-native environment.
- SRE Path: Focuses on the “Service Level.” You use the security skills of the CKS to ensure that attacks don’t impact the availability of your application.
- AIOps/MLOps Path: For those running large-scale data science workloads. You ensure that the complex pipelines running on Kubernetes are safe from data leakage.
- DataOps Path: Focuses on the lifecycle of data. Your CKS skills help isolate sensitive datasets and ensure only authorized processes can touch them.
- FinOps Path: The intersection of security and cost. You learn that over-privileged or insecure systems are often the most expensive to run and maintain.
Role → Recommended Certifications Mapping
| If your role is… | Start with… | Then earn… | Reach the top with… |
| DevOps Engineer | CKA | CKS | DevSecOps Lead |
| SRE | CKA | Monitoring Certs | Observability Master |
| Platform Engineer | CKA | IaC (Terraform) | CKS |
| Cloud Engineer | Cloud Associate | CKA | CKS |
| Security Engineer | CKA | CKS | Advanced Security (CISSP) |
| Data Engineer | Data Platforms | CKA | CKS |
| FinOps Practitioner | FinOps Cert | CKA | Cloud Architecture |
| Engineering Manager | CKA | CKS | Leadership Programs |
Top Institutions for CKS Training
Success in the CKS often depends on the quality of your labs and mentors. These institutions are recognized for their focus on the Kubernetes Security track.
DevOpsSchool offers a very hands-on approach to the CKS. Their instructors focus on the “logic” of security, helping you understand how different components interact. Their labs are designed to be challenging, ensuring you are well-prepared for the actual exam environment.
Cotocus is known for its highly technical and detailed training modules. They provide a deep dive into the specific tools required for the CKS, making them a great choice for engineers who want to go beyond the basics and understand the fine details of cluster hardening.
Scmgalaxy has a long-standing reputation for providing excellent community support and a massive library of technical resources. Their CKS training is built on real-world scenarios, making the learning process very practical and applicable to your daily job.
BestDevOps provides a streamlined training program that is perfect for busy professionals. They focus on the high-impact areas of the CKS exam, ensuring you get the most out of your study time without getting bogged down in unnecessary theory.
Devsecopsschool is dedicated specifically to the security aspect of DevOps. Their CKS training is a core part of their broader security curriculum, making it an ideal place for those who want to make security the primary focus of their career.
Sreschool approaches the CKS from the perspective of system stability. They teach you that security is a prerequisite for reliability, and their training focuses on implementing security measures that don’t negatively impact the performance of your production systems.
Aiopsschool looks toward the future of infrastructure. Their CKS training helps you understand how container security will evolve with the addition of AI-driven monitoring and automated threat response systems.
Dataopsschool provides specialized training for those who manage data workloads on Kubernetes. They focus on the security configurations that are most important for maintaining data privacy and integrity in a containerized world.
Finopsschool connects technical security to financial efficiency. They help you see how a well-secured cluster, with properly managed permissions and resources, is also a much more cost-effective cluster to operate.
FAQs: The CKS Career Path
- How is CKS different from CKA? The CKA is about building and maintaining a cluster. The CKS is about defending it. Think of it as the difference between an architect and a security consultant.
- How long does it take to get the score? Results are typically emailed within 24 hours of completing the session.
- Is the CKS valuable in the Indian job market? Highly. With the rise of global capability centers in India, the demand for certified security specialists is at an all-time high.
- Can I take the exam without the CKA? No. You must have an active CKA certification before you are eligible to sit for the CKS exam.
- Is it a written test? No. It is 100% lab-based. You will be typing commands into a real Linux terminal.
- What is the duration of the certificate? The CKS certificate is valid for 2 years.
- What score do I need to pass? You need a score of 67% or higher to be successful.
- Can I use my own notes? No. You are only allowed to access the official documentation sites listed by the CNCF.
- Are the questions the same every time? No. The questions are randomly selected from a larger pool, making every exam attempt unique.
- Do I get a second chance? Yes, most official exam vouchers include one free retake if you don’t pass on your first try.
- Do I need to be a developer? No, but you must be comfortable with the command line and basic YAML file structures.
- What is the best way to study? Practice in a real cluster. Reading books is fine, but “doing” is the only way to pass this exam.
FAQs: Technical and Exam Logistics
- What Kubernetes version is used? The exam version is updated frequently to stay close to the current stable release of Kubernetes.
- Is the tool “Falco” important? Yes, it is a major part of the runtime security section. You should know how to read and basic rule configurations.
- How much Linux knowledge is needed? You should be very comfortable with basic Linux administration, including file permissions, system logs, and process management.
- Will I have to install anything? You may be asked to install or configure security-related plugins or modify control plane components using
kubeadm. - Is image scanning a big part of the test? Yes. You will likely be asked to use tools like Trivy to find and report vulnerabilities in container images.
- What text editor should I use? Most people use Vim or Nano. You should be fast with whichever one you choose, as you will be editing many files.
- How does RBAC factor in? RBAC is a huge part of the exam. You must be able to create Roles, RoleBindings, and ServiceAccounts with precision.
- Can I search for “Network Policy” during the exam? Yes. If you have the official Kubernetes documentation open, you can search for examples to copy and paste.
Conclusion
The path to becoming a Certified Kubernetes Security Specialist is one of the most rigorous and rewarding journeys in modern engineering. It is not just about passing an exam; it is about adopting a new way of thinking where security is the foundation of everything you build. As a key milestone in the Master in Observability Engineering Certifications Program, the CKS gives you the technical depth to not only see what is happening in your systems but to ensure that what is happening is safe. The challenges—from mastering the Linux kernel to defending against runtime attacks—are significant, but the ability to stand as a guardian for your organization’s infrastructure is an achievement that will define your career for years to come. Whether you are aiming for a lead SRE role or a DevSecOps architect position, the CKS is your proof that you are ready for the highest levels of responsibility in the cloud-native world.